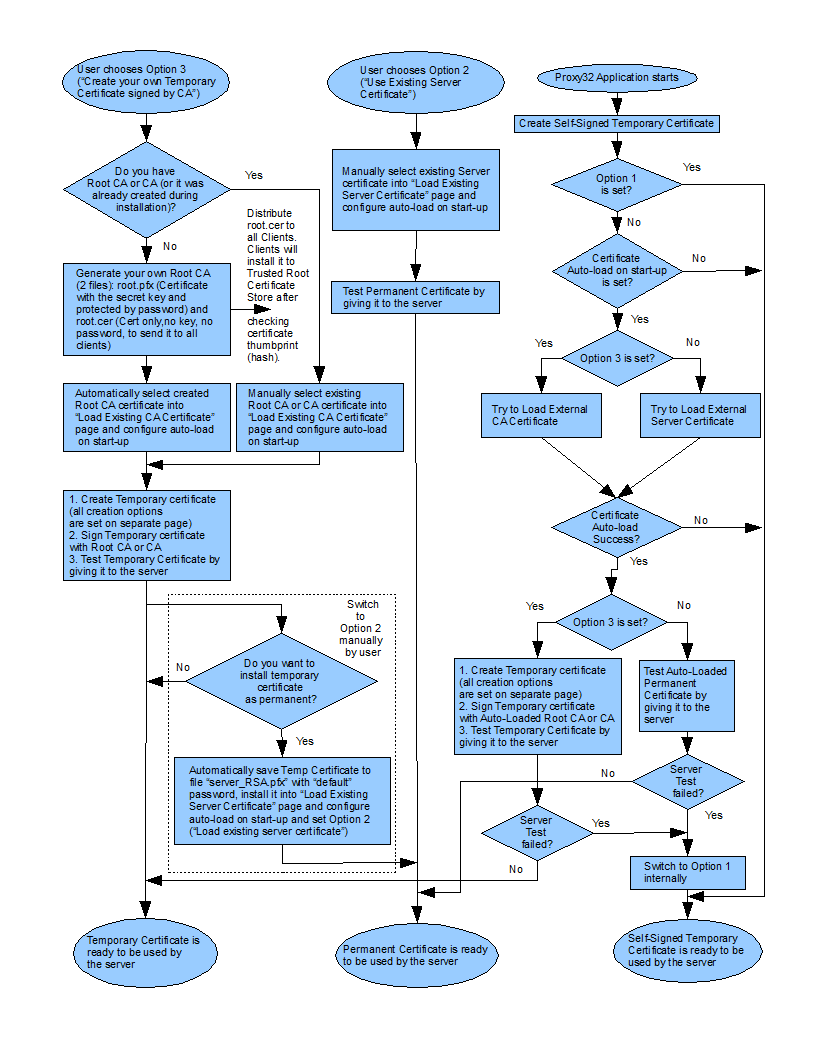
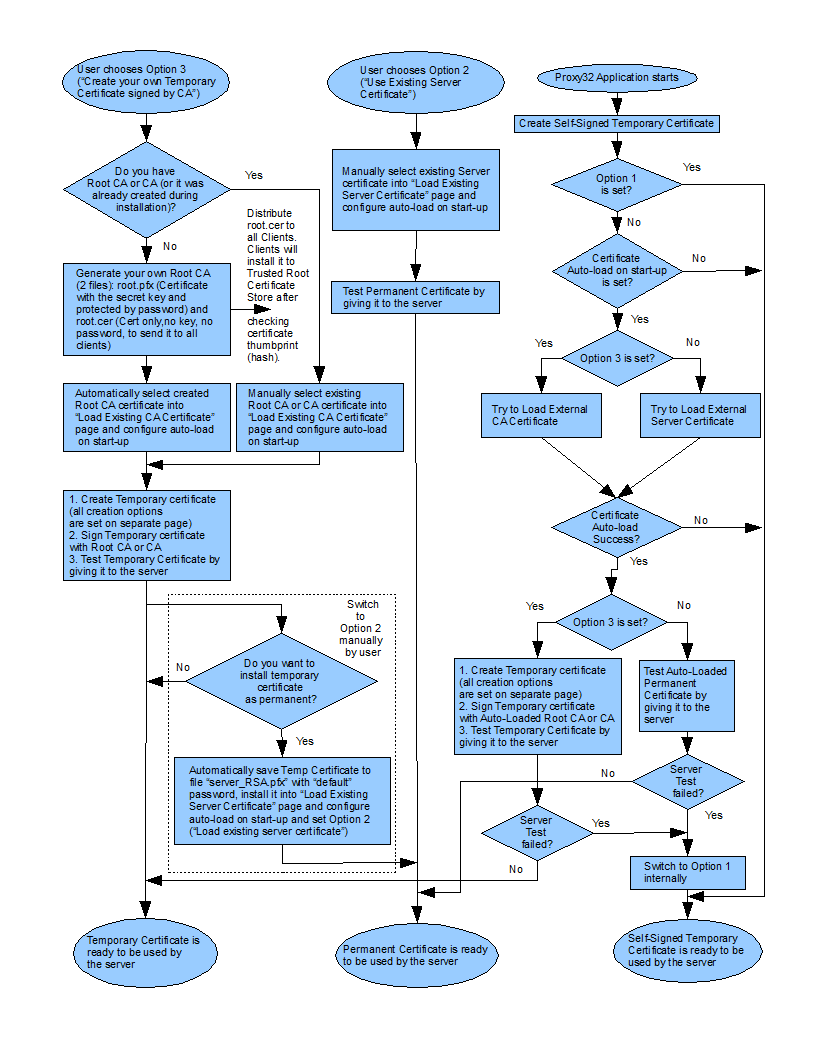
Proxy32 allows following TLS Server certificate options:
Option 1: Temporary Self-Signed Server Certificate:
TLS Server owner does not have to prove Identity of his/her server to anyone, only encryption is desired, but no authentication
-
Without authentication encrypted connection can be intercepted and highjacked by the MAN-IN-THE-MIDDLE.
-
Proxy32 can create Temporary Self-Signed Server certificate on the start and use it for the TLS server.
-
Certificate checking should be disabled in the connecting TLS client.
Option 2: Permanent Server Certificate issued by Commercial or Corporate CA:
TLS Server owner has to prove Identity of his/her server to unlimited number of internet users or corporate users running TLS clients.
-
TLS Server owner has to obtain server certificate (with matching private key) from Commercial or Corporate CA.
-
Certificate (with matching private key) should be installed into Windows System store or into PFX-file.
-
Installed certificate should be configured to autoload on startup and for use by TLS Server.
-
CA Certificate from Commercial or Corporate CA is expected to be already installed as trusted for most existing TLS clients, so no further actions are required to establish trust with TLS Clients
Option 3: Temporary Server Certificate signed by own Root CA certificate:
TLS Server owner has to prove Identity of his/her server to small known group of the users running TLS clients and has to run TLS Server on computer with dynamically assigned IP address
-
TLS Server owner has to create his/her own Root CA certificate (with matching private key) and install it into Windows System store or into PFX-file on the computer running TLS server.
-
Installed Root CA certificate should be configured to autoload on startup.
-
When Proxy32 starts up it will first load configured Root CA Certificate, then it will create Temporary Server certificate and sign it with loaded Root CA certificate.
-
Temporary Server certificate will reflect current public IP address of the server's computer. In the scenario when home router represents public IP address of server's computer, Proxy32 owner should manually enter router's IP address into Proxy32 "Create Temporary Server Certificate" dialog and then manually create new Temporary Server Certificate.
-
To establish trust relation with the internet or corporate users, server owner has to distribute his/her Root CA certificate (without matching private key) to all computers that will run TLS Clients and have this Root CA certificate installed into "Trusted" root CA store on those computers.
Option 4: Permanent Server Certificate signed by own Root CA certificate:
TLS Server owner has to prove Identity of his/her server to small known group of the users running TLS clients and does not want to pay for obtaining commercial server certificate
-
Step 1: Follow Option 3 to create and use Temporary Server Certificate
-
Step 2: After Temporary Certificate is working, it can be installed and configured as permanent server certificate (as described in Option 2) assuming the IP address of the server is permanent.
If all TLS Clients that will be used to connect to the TLS server have capability to selectively disable "server address check on the server's certificate" then Option 2 or Option 4 are the best.