Active Window
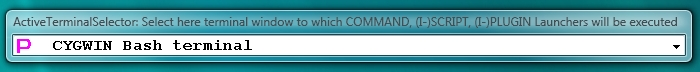
application window inside of the current workspace that all Launchers will try to use when they are executed (double-clicked) on the LauncherTree or via bookmarks. Active window is only applicable for automation launchers (COMMAND/SCRIPT/PLUGIN) because they do not create new window but instead they have to execute into some existing window in the current workspace. Active window is one of the windows inside of the current workspace. If it is Proxy32 window (built-in Proxy32 terminal or built-in proxy32 script editor) then this window will be highlighted by the thick red frame. When window of external process becomes active (PuTTY, MinTTY, Notepad, Firefox, jEdit etc) it will be highlighted with red sticker with the word "ACTIVE" on it that is attached to titlebar of active window. If built-in proxy32 terminal is active, user can execute COMMAND/SCRIPT/PLUGIN into it as long as this terminal is not busy executing previous SCRIPT/PLUGIN, connected and not minimized. If window of external process (PuTTY, MinTTY, Notepad, Firefox, jEdit etc) or built-in proxy32 script editor is active, user can execute COMMAND into it. To make window active user can click on the title of this window or select it from the list of the windows in the current workspace  or from the list of all windows in the Selector window.
or from the list of all windows in the Selector window.
Selector Window Small Font
Autologin
When terminal launchers (SHELL-TERMINAL, TELNET-TERMINAL or COM-PORT-TERMINAL) are executed, they create new window of Proxy32 built-in terminal, connect it to the local shell, server or com-port and then they look for the next launcher on the LauncherTree - immediately under themselves. If any I-SCRIPT or PLUGIN launcher is present immediately under terminal launcher, it is considered to be AUTOLOGIN script for the terminal launcher that is just above it. When terminal launcher successfully connects its terminal window, it will automatically execute its autologin I-SCRIPT or PLUGIN launcher to let it finish login procedure automatically. Typically, autologin script is written to respond to the request for user credentials and to send username and password to the server for the user authentication.